Online privacy has be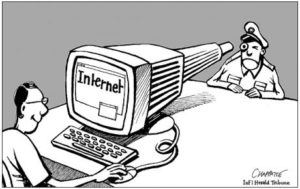 come a very controversial subject in these tumultuous times. Opposing views about privacy and security have clashed, but a talking point that is often brought up is that privacy should not be important to you if you have “nothing to hide,” or as Google chairman Eric Schmidt once infamously put it in an interview: “If you’re doing something that you don’t want other people to know, maybe you shouldn’t be doing it in the first place.” [1] However, this argument is a flawed one, and I will be discussing these flaws in this post.
come a very controversial subject in these tumultuous times. Opposing views about privacy and security have clashed, but a talking point that is often brought up is that privacy should not be important to you if you have “nothing to hide,” or as Google chairman Eric Schmidt once infamously put it in an interview: “If you’re doing something that you don’t want other people to know, maybe you shouldn’t be doing it in the first place.” [1] However, this argument is a flawed one, and I will be discussing these flaws in this post.
Perhaps the biggest flaw in this argument is that most people do, in fact, have something to hide. When I say “something to hide,” I do not mean criminal plots, but rather things that we might not be comfortable with any person knowing. For example, I would imagine one would be uncomfortable if someone could access things like their texts, emails, and web searches, yet these are all things that the NSA has access to. [2]
Furthermore, privacy should be important to you because it is in human nature to seek privacy, because we often act differently when we have a sense of privacy. Even if one says they have nothing to hide, they still lock their doors and close their curtains, or in the case of online privacy, they will still put passwords on their accounts. Take Mark Zuckerberg, who once said that “Privacy is not longer a social norm.” [3] The very same Mark Zuckerberg spent 30 million dollars to buy four properties, in addition to his house, in Palo Alto in order to ensure a zone of privacy. [4] Eric Schmidt of Google even ordered the company’s employees to cease contact with CNET, an online publisher, after CNET published his personal information, which was obtained solely through the use of Google products. [5] Going back to what I said about locking doors and closing curtains, one might argue that those things not be connected to online privacy specifically, but the internet is such an ubiquitous thing that I think this analogy is still apt.
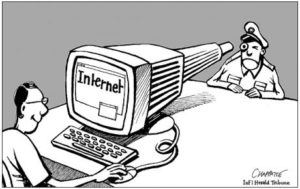
Privacy is not just a personal good, it is also a social good. Privacy allows for one to dissent without fear. If there was no privacy, there would be no room for dissent, only conformity. Thus, there would be social change. This is outlined in George Orwell’s 1984, cliche an example as it is. In the novella, Big Brother’s tyranny is able to be accomplished since everyone must assumed they are being watched, and are thus powerless to resist.
The final, and perhaps most dangerous part of this argument is the dichotomy it establishes between “good” people who have nothing to hide, and “bad” people who do. As What makes this mindset concerning is that it condemns those who are not willing to surrender their privacy, and suggests that one must relinquish their privacy to free themselves of suspicion. It villainizes the perfectly reasonable desire for privacy, and people who use it to bring about change. Thanks for reading.